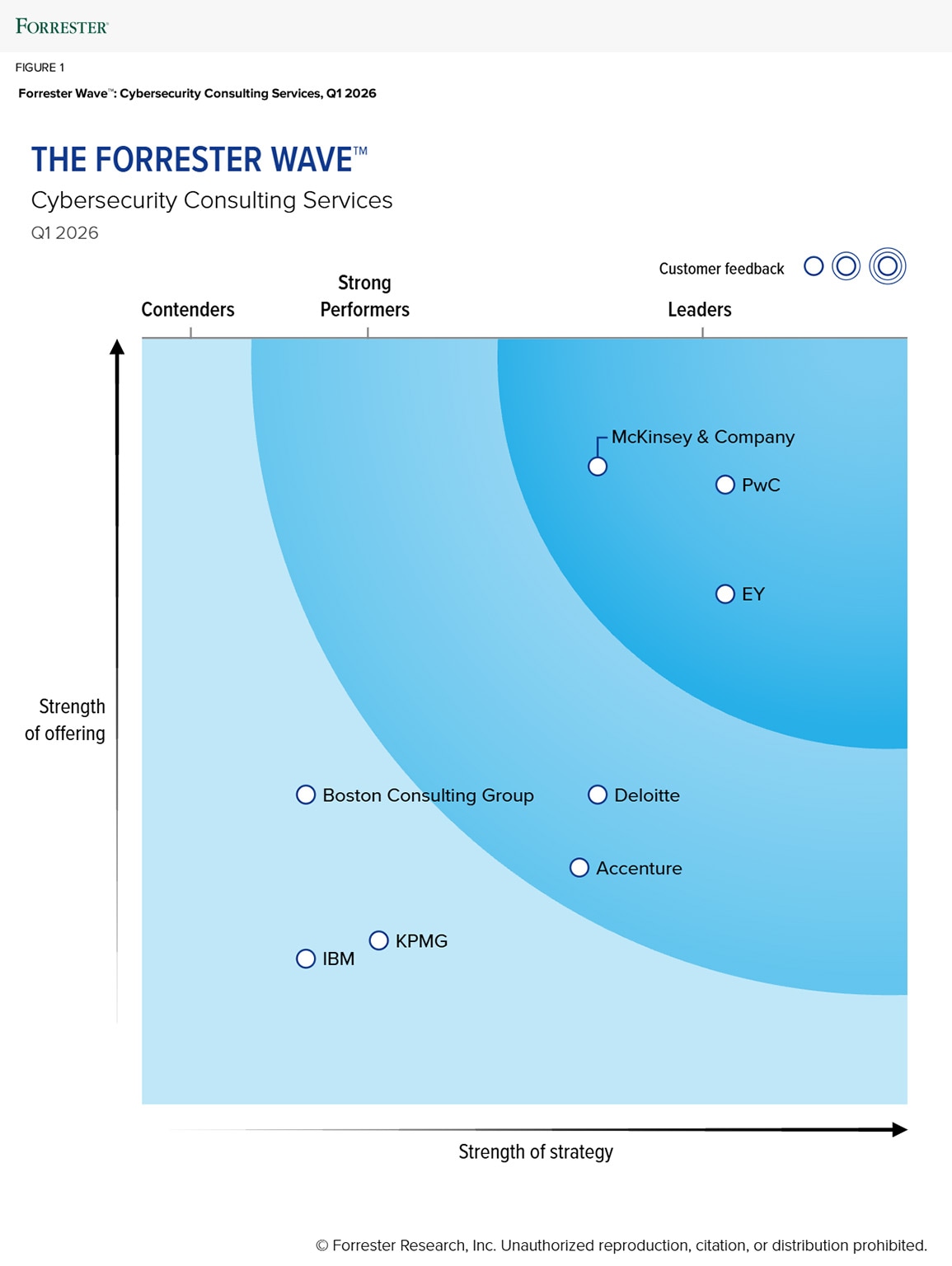
McKinsey named a Leader in Cybersecurity Consulting Services by Forrester
Forrester recognized McKinsey as a Leader in cybersecurity consulting services, the highest designation possible in The Forrester Wave™: Cybersecurity Consulting Services, Q1 2026.
A reprint of the full Forrester Wave report can be found here.
“McKinsey elevates cybersecurity to a board-level priority, embedding risk-to-value narratives into enterprise decision-making. Its vision and advisory depth are clear differentiators, supported by gen-AI-enabled delivery and regulatory foresight,” the Forrester report states.
Forrester evaluated eight providers on 20 criteria of current offering and strategy, with McKinsey receiving the top score of all vendors evaluated in the current offering category, including:
- Alignment with CISO needs
- Executive engagement
- Engagement staffing and resource allocation
- Knowledge transfer and training
- AI-empowered service delivery
- AI security and governance
- Security posture and program maturity
- Security strategy and roadmap development
- Security tech stack consolidation and optimization
- Security budget optimization
The report goes on to state, “McKinsey stands out for strategic clarity and maturity benchmarking through proprietary assets and methodologies. Gen AI tools such as Lilli accelerate analysis and control mapping, accelerating time to value.”
We recently caught up with Charlie Lewis, the McKinsey partner who leads our cybersecurity team in North America and Europe to learn more about how McKinsey is helping its client address an ever-evolving threat landscape.
What does this Forrester ranking of a ‘Leader’ in cybersecurity consulting services mean for you?
We are proud to receive this external recognition as it is a meaningful milestone for our global team. More importantly, it reinforces what we consistently hear from our clients: they value our distinctive ability, and our investments in emerging technology, to connect their strategic priorities across the board, CEO, and executive leadership team—with deep technical expertise and execution—as we seek to be their strategic cyber counselor.
Our McKinsey team spans the globe serving the world’s most iconic and critical companies, with practitioners representing areas of digital, risk, and cloud. Our approach is unique, in that we: 1) believe cyber is a strategic differentiator when empowered to enable the business; 2) take a business-back approach to driving impact, creating value to address every aspect of security; 3) and embed the full power of McKinsey in our cyber delivery model using our industry expertise, reach and collaboration, proprietary assets, and innovation through new technologies.

How are organizations adjusting to new threats?
Organizations recognize that the threat landscape is accelerating, and that attackers operate like sophisticated businesses. Companies are investing in R&D, optimizing for return on investment, and increasingly leveraging generative and agentic AI to scale and sharpen their posture. We see three trends:
- Treating AI as both opportunity and threat: Leading companies understand that for every AI investment they make, attackers will do the same. Generative AI is already accelerating social engineering through more convincing phishing, automated campaigns, deepfakes, and rapid code generation. Less-skilled malicious actors can now use AI tools to produce effective attack code. Organizations are therefore focusing on securing their own gen AI systems, stress-testing them for misuse, and anticipating how adversaries may exploit them, especially as they scale their agentic builds.
- Preparing for quantum risk: While gen AI poses the more immediate risk acceleration, quantum computing introduces long-term concerns, particularly the “harvest now, decrypt later” dynamic, where attackers store encrypted data today in anticipation of breaking it in the future. Companies are assessing cryptographic exposure and planning for future hardening based on a risk-based approach.
- Shifting to integrated threat response: Forward-looking organizations are breaking down silos and creating “fusion” capabilities that combine cyber operations, technology operations, fraud, AML, and even physical security signals. This integrated view allows faster context-building and more coordinated response to emerging threats. Overall, the adjustment is less about chasing every new threat trend and more about building adaptive, business-aligned resilience.

Cybersecurity
Establishing cyber resiliency and implementing a cybersecurity strategy aligned with the organization’s priorities
How should an organization create a strong cyber foundation?
Foundations matter more than ever. You cannot innovate securely without first stabilizing the base. While AI dominates headlines, many breaches still trace back to basic weaknesses. Organizations are therefore refocusing on asset visibility, “If you don’t know what you have, you can’t secure it;” identity and access management and understanding who has access, how identities move through networks, and enforcing strong authentication controls, especially knowing that identity is the control plan of today and the future; vulnerability management at scale, and not just addressing individual vulnerabilities, but building a systemic view across the environment to identify concentration risks and weaknesses; risk-based prioritization, rather than spreading controls evenly across everything, leading organizations focus on critical business processes and high-impact assets, and finally, technical debt reduction, where organizations address legacy systems and end-of-life technology, or “tech debt,” where building advanced AI capabilities on top of weak foundations only increases long-term cost and risk.
You cannot innovate securely without first stabilizing the base.
How is cybersecurity like an ice cream sandwich?
I have an analogy that cybersecurity operates like an ice cream sandwich, illustrating the concentration of risk in supply chains and critical business processes. An ice cream sandwich has three core components, the wrapper, the ice cream, and the wafer.
If a cyberattack disrupts even one of those components, for example a supplier of dairy or packaging, the entire product supply chain can be halted. That disruption does not just affect the manufacturer; it cascades downstream, potentially impacting distributors, retailers, and even the local ice cream truck. There are three lessons here:
- Identify your critical components: Know what truly matters to delivering your product or service and build knowledge of these as “nodes”
- Understand third- and nth-party dependencies: Risk often sits beyond direct suppliers, especially when thinking about the critical nodes and horizontal dependencies
- Assess concentration risk: If one vendor failure halts operations, an organization has a structural vulnerability for its resilience. If one vendor at the fourth- or fifth-party level can impact more business processes, the cascading failure will have longer and more lasting effects.
In short, cybersecurity is not just about protecting internal systems. It is about protecting the integrity of the entire ecosystem that enables your core business.
Forrester does not endorse any company, product, brand, or service included in its research publications and does not advise any person to select the products or services of any company or brand based on the ratings included in such publications. Information is based on the best available resources. Opinions reflect judgment at the time and are subject to change. For more information, read about Forrester’s objectivity here. A reprint of the full Forrester Wave report can be found here.

